Blockchain
5 Reasons Why Delta Exchange is the Easiest Platform for Crypto Trading Strategies in the Indian Market

Crypto trading in India has grown exponentially in the last few years. In 2025, the market pulled in $258 million in revenue and is on track to hit nearly $732 million by 2033, growing at a 14.3% CAGR from 2026 onwards. That kind of money doesn’t come from people buying Bitcoin on a whim and hoping for a lucky spike. It comes from traders who plan entries, manage exits, build hedges, and run full-blown crypto trading setups.
This shift has created a new problem. Most Indian crypto exchange apps still feel built for basic spot buying without any advanced features to try. You open five tabs, check prices on one app, place orders on another, track risk on a third, and hope nothing slips through.
Delta Exchange transforms the story here. Instead of spots, Delta offers a safe trading platform to explore crypto derivatives (futures and options) across major currencies.
Let’s understand more about Delta Exchange and why so many Indian traders end up sticking with it once they try it.
Why Try Crypto Trading Strategies on Delta Exchange
Ranked among the top Indian crypto exchanges, Delta Exchange offers a range of features and analytics tools to simplify your crypto trading experience.
Here’s why many traders trust Delta Exchange:
- INR trading keeps things simple
If you’ve ever had to convert INR to USDT or USD just to trade Bitcoin, you know the hassle. Delta Exchange lets you deposit and withdraw in INR directly via UPI, IMPS, NEFT, and bank transfer, with your margin and profits shown in INR.
That means no awkward crypto conversions or extra wallets – you fund your account straight from your bank and start crypto trading like it’s normal money.
- Algo trading bots that actually work
Automation can save hours and reduce emotional stress and decisions, especially with fast moves in crypto F&O. Delta Exchange supports algo trading through APIs and bot integrations from platforms like TradingView and Tradetron.
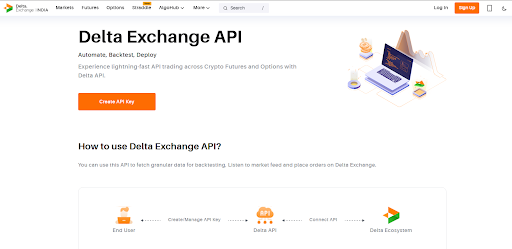
You can link your trading strategy to webhooks or APIs and let bots place trades for Bitcoin futures or other crypto options even when you’re away. If you want systematic, repeatable strategies with fewer missed opportunities, this setup feels practical and real.
And the best part? You don’t need to have any coding knowledge or degree – API Copilot does it all for you.
- Lower trading fees that don’t eat into your wins
Fees matter because every percentage point you pay is one less in your pocket after a winning trade. Delta Exchange offers competitive taker and maker fees, plus a fee cap on options that limits how much you pay on low premium trades.
This helps keep costs predictable, whether you’re trading Bitcoin or ETH futures and options. Traders who place frequent trades or use multi-leg strategies on the Indian crypto exchange can keep more of their gains, rather than having them eaten up by trading fees.
- Strategy Builder for practical trading plans
Strategy planning can get messy if the platform doesn’t help you visualize outcomes. Delta Exchange offers tools that let you craft crypto F&O setups with clear strike choices and expiries, plus daily, weekly, and monthly options for more precise timing. This helps you conveniently plan spreads, straddles, or hedges.
- Compliance and risk measures to know
It’s one thing to trade, another to trust the platform doing it. Delta Exchange is registered with India’s Financial Intelligence Unit (FIU) and follows local KYC and AML rules.
For risk management, the platform supports:
- Margin controls and stop-loss tools that help you manage positions while you trade Bitcoin or other crypto derivatives.
- Demo account to practice trades and understand the market without real money.
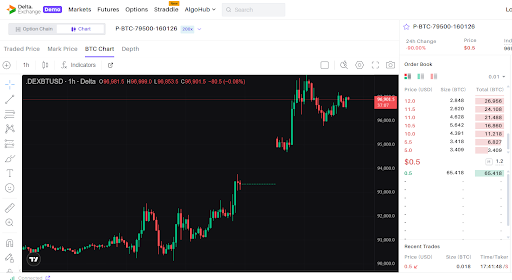
- Payoff charts show you how your trade will play out with breakeven points and maximum P&L.
This way, you can study your crypto trading strategy better before finalizing the trade.
Apart from these, Delta also offers leverage up to 200X – a good way to amplify your profits if the market moves in your favor.
The Bottomline
Indian crypto traders have moved far past the buy-and-hold phase. Spot crypto trading still has its place, yet most active users now want faster ways to make money from price swings, not wait months for a rally.
That’s where crypto F&O, spreads, and short-term setups step in. You want tools that let you react within minutes, control risk, and lock gains when the move shows up.
Platforms that only support basic coin buying just can’t keep up with that style of trading. Serious traders want flexibility, speed, and ways to work with volatility, not sit through it – and Delta Exchange caters to such traders well.
Disclaimer: Crypto trading carries inherent risks due to its high volatility. This article is for informational purposes only. Kindly do your own research before making any investment decisions.
Blockchain
ERC-7943 Enters Final Status as Ethereum’s Framework for Real-World Asset Tokenization

The Universal Real-World Asset (uRWA) standard is now specification-frozen and ready for production adoption across Ethereum and EVM-compatible networks
ERC-7943, the Universal Real-World Asset (uRWA) standard, has reached Final status within Ethereum’s formal standards process. The specification is now frozen – with its interface, error definitions, event signatures, and behavioral requirements fixed – and is available for production adoption across Ethereum and EVM-compatible networks.
ERC-7943 defines a minimal, vendor-neutral interface for the compliant tokenization of real-world assets. The standard addresses transfer validation, asset freezing, forced transfers, and enforcement actions without binding implementers to a specific identity provider, jurisdictional framework, or compliance stack. This approach enables institutions and developers to deploy regulated assets across jurisdictions while retaining flexibility over underlying compliance infrastructure.
“ERC-7943 gives institutions and developers a modular interface for compliance, transfer controls, and enforcement, so they can deploy regulated assets in any jurisdiction without depending on a single vendor’s stack,”
said Dario Lo Buglio, lead author of ERC-7943. “Compliance becomes pluggable since the standard separates the on-chain interface from the underlying KYC, sanctions, and jurisdiction logic.”
Final status represents the threshold for enterprise adoption in Ethereum’s standards process, as proposals may undergo substantial changes before reaching this stage. ERC-7943 attained Final status following multiple cycles of community review through Ethereum Magicians and the EIP working group. With the standard now finalized, institutions and infrastructure providers can build on a stable specification designed for long-term interoperability.
Early adoption is already underway. The Capital Markets and Technology Association (CMTA) has integrated ERC-7943 into recent releases of CMTAT, its open-source tokenization framework deployed in institutional initiatives globally. Chainlink has separately demonstrated compatibility through a public pull request tied to its Asset Compliance Engine (ACE). Brickken plans to integrate ERC-7943 into upcoming institutional infrastructure upgrades, with the standard expected to become the default framework across its product suite. These developments signal a transition from specification to active deployment across infrastructure and compliance environments.
The coalition supporting ERC-7943 has grown since its September 2025 announcement and now spans the full RWA stack, encompassing issuance platforms, infrastructure providers, exchanges, marketplaces, identity vendors, and audit firms. Backers and contributors include Bit2me, Brickken, Casper Network, CMTA, Compellio, Dekalabs, DigiShares, Forte Protocol, FullyTokenized, Propchain, RealEstate.Exchange, Stobox, and Zoth. Hacken and QuillAudits serve as security and audit partners.
The standard is open for adoption by issuers, infrastructure providers, and developers building tokenized financial instruments. Documentation, reference implementations, and community channels are available at erc7943.org. The full specification is published at eips.ethereum.org/EIPS/eip-7943.
About Bit2me
Bit2Me is the leading cryptoassets company in Spain, registered with the CNMV as a Crypto Asset Service Provider (CASP). The company has been building crypto infrastructure for more than 10 years and holds several cybersecurity and regulatory compliance certifications, including: ISO 27001 for Information Security Management; ISO 22301 for Business Continuity Management; ISO 37001 for Anti-Bribery and Corporate Ethics; ISO 37301 for Compliance Management Systems; UNE 19601 for Criminal Compliance Management Systems; and the CSA STAR Level 1 certification. https://bit2me.com/
About Brickken
Brickken is a global leader in the tokenization of real-world assets, offering a comprehensive SaaS platform that enables businesses to tokenize equity, debt, and revenue-sharing models. By integrating traditional finance with blockchain technology, Brickken provides tools to simplify asset management, enhance investor engagement, and unlock liquidity. With over $500 million in tokenized assets and a presence in 30 countries, Brickken is at the forefront of innovation in asset tokenization. To learn more about Brickken, visit www.brickken.com/
About Compellio
Compellio SA is a deeptech company headquartered in Luxembourg providing global infrastructure components for bridging the gap between web2 and web3 computing. Based on its patented technology, Compellio works with public and private organisations in driving regulatory-compliant solutions across multiple industries. Compellio’s tokenisation platform enables developers to abstract away the complexity of smart contracts and build standardised interoperability frameworks for the lifecycle management of their physical, digital, and hybrid assets. For more information, visit https://compellio.com
About Dekalabs
Dekalabs is a Valencia-based software development and digital transformation consultancy specializing in cutting-edge blockchain solutions. With a multidisciplinary and senior technical team, they deliver bespoke services spanning mobile applications, web applications, corporate solutions, UI/UX, and artificial intelligence (dekalabs.com).
About DigiShares
DigiShares is a market-leading provider of white-label software for the compliant issuance, management, and trading of tokenized real-world assets. The platform enables asset owners and fund managers to fractionalize assets, onboard global investors at low cost, and provide peer-to-peer or exchange-based liquidity through integrations with regulated venues such as RealEstate.Exchange. With more than 200 clients worldwide, offices in the US and Denmark, a network of 80+ legal partners, and integrations across Ethereum, Polygon, and other EVM chains, DigiShares offers one of the most flexible and customizable solutions in the industry. See www.digishares.io.
About Hacken
Hacken is an end-to-end blockchain security & compliance partner for digital assets. Unlike traditional providers, Hacken was born on blockchain. We combine deep Web3 expertise with enterprise-grade quality, AI-powered offensive security, and globally recognized certifications. Since 2017, Hacken has been trusted by 1,500 adopters including the European Commission, ADGM, MetaMask, Ethereum Foundation, and Binance to secure the new digital frontier. Visit www.hacken.io
About the Forte Protocol
The Forte Protocol is a next-generation blockchain infrastructure that unlocks tokenized economies, enabling developers to define, launch, and monetize their on-chain projects. Through its ecosystem of products and services, Forte Protocol is the infrastructure layer for safe, enduring digital economies that generate long-term value for developers and users. For more information, visit ForteFoundation.io
About FullyTokenized
FullyTokenized is a boutique development company specializing in custom blockchain, tokenization, and Web3 solutions. With a proven track record of delivering successful projects in highly regulated financial environments, including for Fortune Global 500 institutions, the company has contributed to projects representing more than $500M in tokenized value. FullyTokenized also empowers Web3 startups, helping them launch products in under 90 days and scale within the decentralized ecosystem. Visit https://www.fullytokenized.com to learn more.
About Propchain
Propchain is the technology vertical of Prop.com, building institutional-grade infrastructure for real estate financing and tokenized capital markets. Backed by Prop.com’s ~$150M in AUM and active operations across Europe and the UAE, Propchain connects real-world deal flow to digital rails for origination, compliant issuance, lifecycle servicing, investor reporting, and secondary distribution. The company is building one of the world’s first fully unified, standardized, verified data infrastructure layers for real estate—harmonizing operational, financial, and legal data into auditable records that enhance underwriting, monitoring, and transparency. Securitisations are issued out of Luxembourg, aligning with European regulatory frameworks and institutional best practice. Propchain’s product suite, including PropYield, is purpose-built to bridge high-quality real assets with modern market infrastructure, enabling scalable access to real estate yield while preserving rigorous compliance, governance, and data integrity.
About RealEstate.Exchange
RealEstate.Exchange (REX) is the world’s first licensed and regulated exchange purpose-built for tokenized real estate shares. REX combines decentralized finance technology with full compliance layers, enabling investors worldwide—both retail and institutional—to trade tokenized real estate shares directly from their self-custodial wallets. The platform offers instantaneous atomic-swap settlement, competitive listing fees, and a liquidity framework supported by the BRICK token. With its global legal network and partnerships with licensed entities, REX aims to become the go-to venue for secondary trading of tokenized real estate, see www.realestate.exchange.
About Stobox
Stobox is a turnkey asset tokenization provider and technology company focused on building the infrastructure for compliant digital assets. It enables businesses and individuals to transform real-world assets into tokenized instruments that are transparent, liquid, and accessible. Core solutions include Stobox 4 for token issuance and management, the STV3 Protocol for compliant token frameworks, Stobox DID for digital identity, and the Stobox Oracle for real-world data integration. Its structured methodology supports issuers across every stage of the tokenization lifecycle, from legal readiness to fundraising and secondary markets. Companies benefit from streamlined access to capital and global investors, while investors gain exposure to previously illiquid opportunities. https://www.stobox.io/
About Zoth
Zoth is reimagining global finance with the world’s first full-stack, modular Stablecoin Operating System, enabling enterprises and institutions to launch stablecoins and tokenized RWAs 90% faster and 70% cheaper. Its core products include FAAST (compliant tokenization infrastructure), Stablecoin Studio (stablecoin-in-a-box), ZeUSD (yield-bearing stablecoin), and PayX7 (stablecoin payments infrastructure).
Zoth delivers a full-stack suite spanning tokenization, payments, and yield management, supported by BVI & CIMA-regulated fund structures across 127 countries. Recognized by Messari as a top player in PayFi and RWAFi, Zoth combines compliance, scalability, and innovation to power the future of real-world finance. Visit https://zoth.io/.
Blockchain
LayerZero Blames Kelp Setup for $290M Exploit as Aave Fallout Deepens

The fallout from the recent Kelp DAO exploit continues to ripple across the crypto ecosystem, with LayerZero pointing to a flawed system setup as the root cause of the attack.
Single Point of Failure Led to Exploit
LayerZero said the breach stemmed from how Kelp DAO configured its decentralized verifier network (DVN).
The attacker drained roughly 116,500 rsETH, valued at nearly $293 million, from Kelp’s LayerZero-powered bridge.
According to LayerZero:
- Kelp relied on a 1/1 DVN setup, meaning only one verifier was used
- This created a single point of failure
- Prior recommendations to diversify verifiers were not followed
As a result, the attacker was able to exploit the system without needing to bypass multiple verification layers.
LayerZero Distances Itself
LayerZero stressed that the issue was not a flaw in its protocol, but rather how Kelp implemented it.
The company is now:
- Urging all projects to adopt multi-DVN configurations
- Warning it may stop supporting apps that continue using single-verifier setups
Aave Hit With $195M in Bad Debt
The impact quickly spread to Aave, where the attacker used stolen assets as collateral to borrow funds.
This led to:
- Around $195 million in bad debt
- A sharp drop in Aave’s total value locked
- Billions withdrawn by users amid rising concerns
Liquidity issues have also emerged, especially around Ether-based lending pools.
Liquidity Risks Raise Alarm
Reduced liquidity on Aave is now creating additional risks.
Analysts warn that:
- Markets are nearing 100% utilization
- A 15% to 20% drop in Ether price could trigger further instability
- Liquidations may fail under current conditions
To limit further damage, Aave has frozen rsETH markets across its platforms.
Who Covers the Losses?
With no clear recovery plan, debate has intensified over who should absorb the losses.
Suggestions from industry figures include:
- Negotiating with the attacker for a partial return of funds
- Using ecosystem funds to cover losses
- Spreading losses across users
- Attempting a rollback to pre-hack balances
Each option carries trade-offs, and no consensus has emerged.
Broader Implications for DeFi
The incident highlights how interconnected DeFi protocols can amplify risk.
A vulnerability in one protocol can quickly:
- Spill into lending markets
- Trigger liquidity crises
- Impact multiple platforms simultaneously
Security Practices Under Scrutiny
LayerZero’s criticism of Kelp’s setup underscores a key lesson: security configurations matter as much as the underlying technology.
As protocols grow more complex, ensuring robust multi-layer verification systems may become essential to preventing similar exploits.
Blockchain
Privacy Protocol Umbra Shuts Down Front End to Disrupt Hackers
Privacy-focused crypto protocol Umbra has temporarily taken its front-end interface offline in an effort to slow down hackers attempting to move stolen funds.
The move comes amid heightened scrutiny following a series of major exploits across the crypto ecosystem.
Front-End Taken Offline After Suspicious Activity
Umbra said it identified roughly $800,000 in stolen funds being routed through its protocol. In response, the team placed its hosted front end into maintenance mode.
The protocol noted that the interface will remain offline until it is confident that restoring it will not interfere with ongoing recovery efforts.
This action follows the recent exploit of Kelp DAO, where attackers stole over $280 million, with some reports linking the movement of funds through Umbra.
Limits of Control in Decentralized Systems
Despite shutting down its front end, Umbra acknowledged a key limitation: it cannot stop users from interacting directly with its smart contracts.
Because the protocol is open-source:
- Users can access it through self-hosted interfaces
- Alternative front ends can be deployed independently
- Smart contracts remain fully operational onchain
This highlights the broader challenge of controlling decentralized infrastructure once it is live.
Debate Over Responsibility Intensifies
The situation has reignited debate around developer responsibility in decentralized systems.
Roman Storm, co-founder of Tornado Cash, argued that disabling a front end may not be enough to satisfy regulators.
Storm, who was previously convicted in a high-profile case, said authorities may still view control over a user interface as control over the protocol itself.
He warned that:
- Modifying or shutting down a front end could be interpreted as governance authority
- Developers may still face legal accountability regardless of decentralization claims
Umbra Defends Its Design
Umbra pushed back on claims that its protocol is useful for laundering funds.
The team emphasized that:
- The protocol primarily protects the receiver’s identity, not the sender’s
- Transactions remain traceable onchain
- Stolen funds routed through Umbra can still be identified
It also confirmed that it is working with security researchers to track suspicious activity.
Ongoing Pressure on Privacy Tools
The incident reflects growing pressure on privacy-focused crypto tools as regulators and law enforcement target illicit fund flows.
While some platforms have taken steps to freeze or block hacker activity, decentralized protocols like Umbra face structural limitations in enforcement.
A Balancing Act Between Privacy and Security
Umbra’s decision underscores a broader tension in crypto:
- Preserving user privacy
- Preventing misuse by bad actors
As exploits continue and scrutiny increases, protocols may face tougher choices around how much control they can or should exert over their systems.
-

 Crypto4 years ago
Crypto4 years agoCardalonia Aiming To Become The Biggest Metaverse Project On Cardano
-
 Press Release6 years ago
Press Release6 years agoP2P2C BREAKTHROUGH CREATES A CONNECTION BETWEEN ETM TOKEN AND THE SUPER PROFITABLE MARKET
-

 Blockchain6 years ago
Blockchain6 years agoWOM Protocol partners with CoinPayments, the world’s largest cryptocurrency payments processor
-

 Press Release6 years ago
Press Release6 years agoETHERSMART DEVELOPER’S VISION MADE FINTECH COMPANY BECOME DUBAI’S TOP DIGITAL BANK
-

 Press Release5 years ago
Press Release5 years agoProject Quantum – Decentralised AAA Gaming
-

 Blockchain6 years ago
Blockchain6 years agoWOM Protocol Recommended by Premier Crypto Analyst as only full featured project for August
-

 Press Release6 years ago
Press Release6 years agoETHERSMART DEVELOPER’S VISION MADE FINTECH COMPANY BECOME DUBAI’S TOP DIGITAL BANK
-

 Blockchain6 years ago
Blockchain6 years ago1.5 Times More Bitcoin is purchased by Grayscale Than Daily Mined Coins